Limited Access with Sensitivity Labels for Unmanaged Devices
If you’ve read my earlier blog post, you know that Conditional Access can also enforce limited web-only access for unmanaged devices. However, if you don’t want these restrictions to apply to all corporate data and instead want to protect specific locations with sensitive or business-critical information, enforcing limited web-only access with Sensitivity Labels could be the solution. Identifying which locations to protect may be challenging, but Sensitivity Labels can help make these access controls more user-friendly and targeted.
This blog will include the following sections;
- Preparation
- Configure Sensitivity Label
- Verify tenant access control setting
- Configure Conditional Access policy
- Configure Sensitivity Label policy
- Apply labels to sites (as an admin)
- Apply labels to sites (as an user)
- User Experience
In this blog post, I will guide you through the steps and share my experience on how to use Sensitivity Labels to configure limited web-only access for unmanaged devices.
Preparation
Let’s start with some basic licensing requirements;
- M365 E3/E5, O365 E3/E5, EMS E3/E5 or Business Premium subscription; for implementing Sensitivity Labels.
- Azure Active Directory Plan 1 license; for implementing a Conditional Access policy.
- Microsoft Intune license; for managing corporate devices.
- SharePoint Online license; for users accessing the company data.
Most companies won’t have to worry about licensing as long as they have a Business Premium or M365 E3 subscription, as these subscriptions are sufficient to cover all the licensing requirements.
Then, for some recommendations, I would like to ask you the following questions;
- Are all users working from corporate devices, or are some of them using personal devices? If users are using unmanaged personal devices, be prepared for them to have web-only access while accessing data.
- Are users primarily using the Microsoft Edge browser, or have you implemented Single Sign On for alternative browsers like Google Chrome and Firefox? If not, users will have limited web-only access when using these browsers on managed devices.
- Have you integrated Azure AD B2B with SharePoint and OneDrive to ensure guests can be included or excluded from Conditional Access policies?
I recommend reading my previous post if you have any concerns about the above. It includes more information on how to deal with these concerns and can provide you with a better understanding of how the app-enforced restrictions setting works.
Configure Sensitivity Label
To get started, make sure that you have enabled support for Sensitivity Labels specifically for containers. If you haven’t enabled this feature, you won’t be able to create Sensitivity Labels for your SharePoint Sites and Microsoft Teams. You can refer to my quick guide for a step-by-step process on how to enable this feature.
Let’s move on to the most important part of this post, which is configuring the Sensitivity Label. This label can be applied to specific SharePoint or team sites to enforce limited web-only access for unmanaged devices.
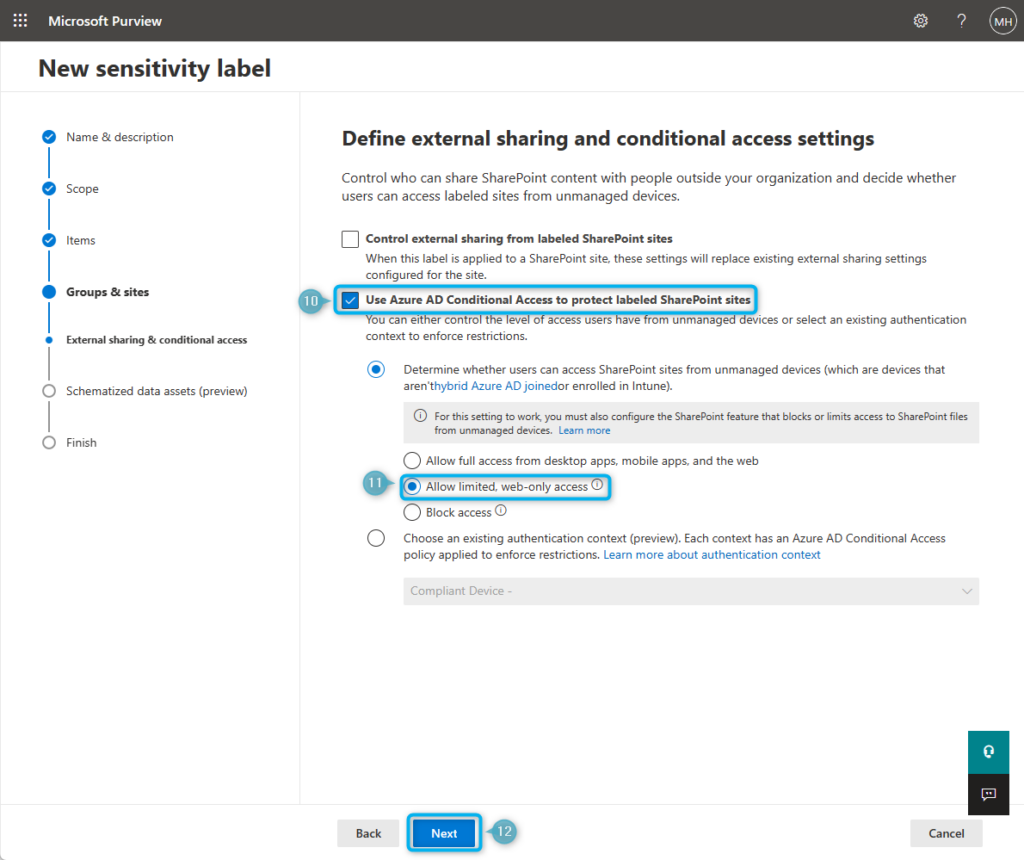
Follow these steps to configure the Sensitivity Label;
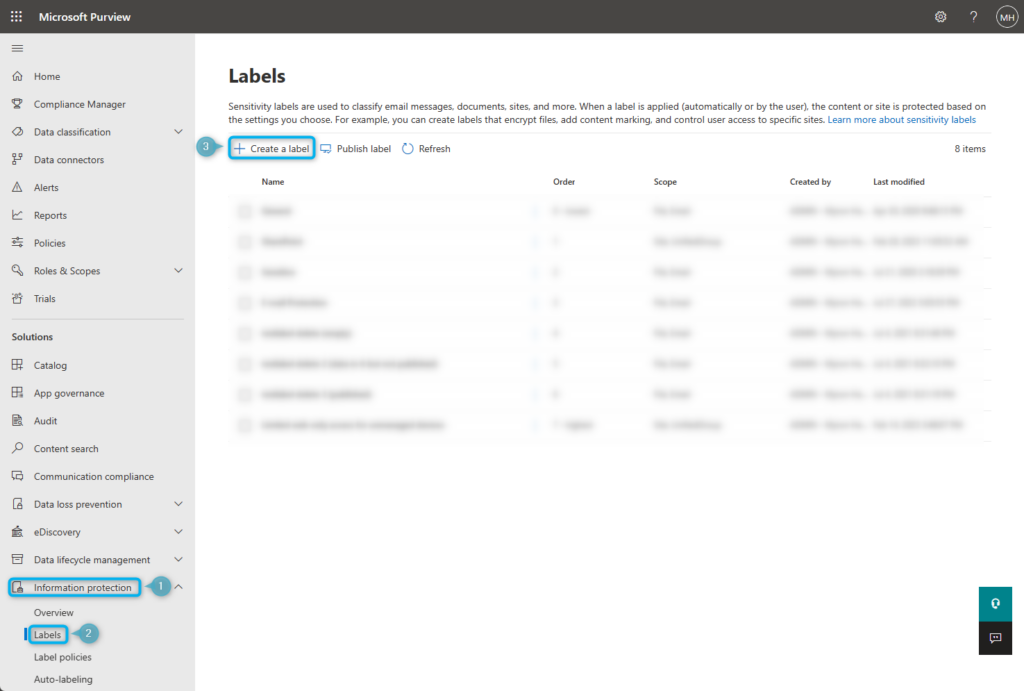
- Go to Microsoft Purview (former Compliance Admin Center) and navigate to Solutions > Information Protection.
- Go to the Labels page.
- Click on + Create a label, to create a new sensitivity label.
Optional: You can also create a sub-label if you already use sensitivity labels.
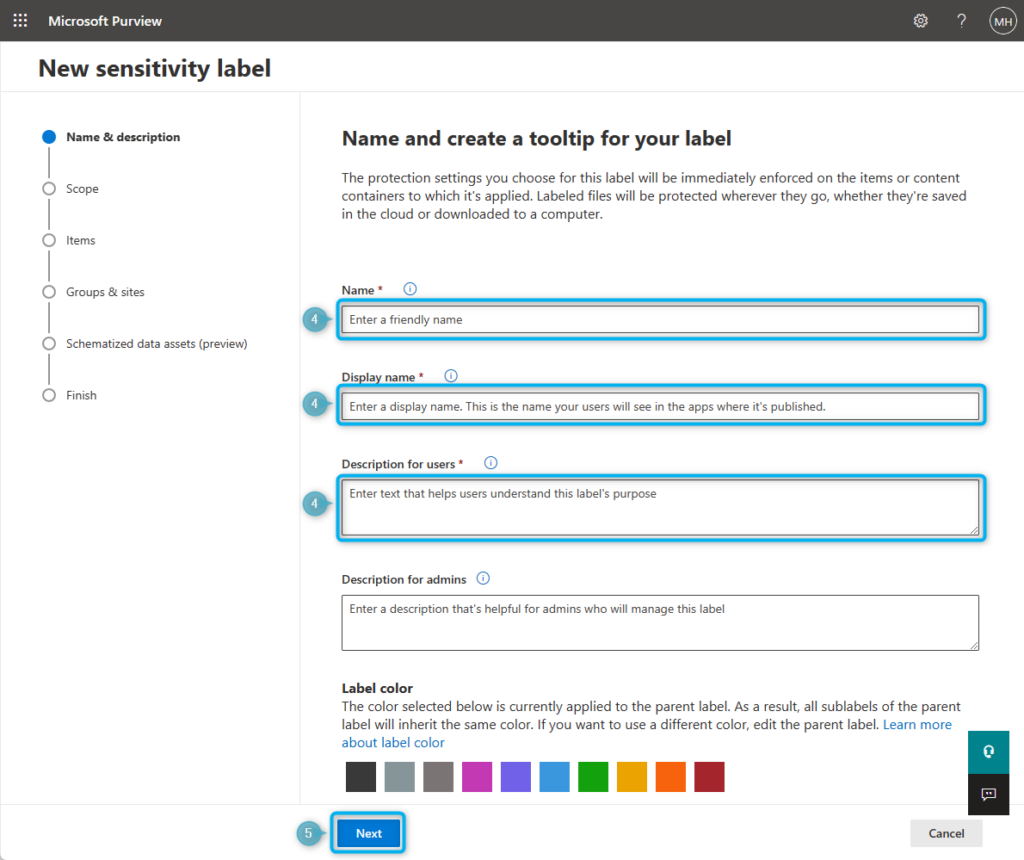
- Enter a Name, Display name, and a Description for users that fits your company’s labeling naming convention and strategy.
Optional: Enter a Description for admins or Label color.
- Click Next.
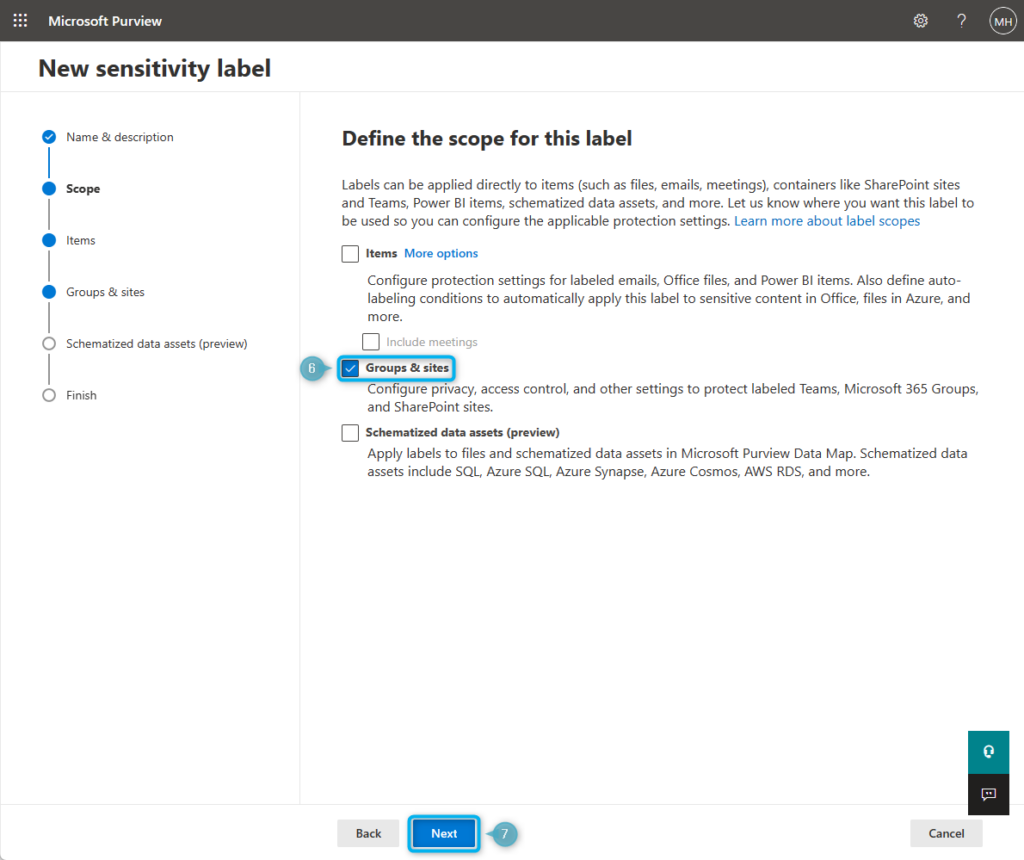
- Select Groups & sites. (The Groups & Sites option being greyed out indicates that container support for Sensitivity labels has not been enabled yet)
- Click Next twice. (skip the Items page)
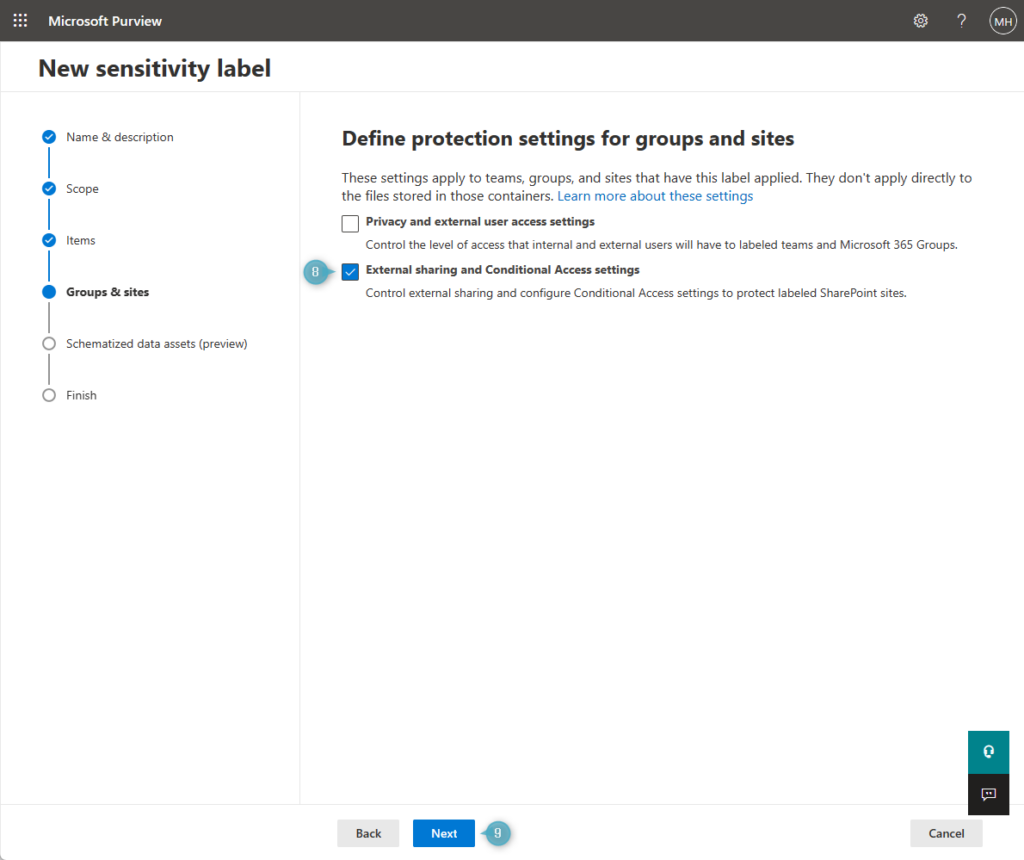
- Select External sharing and Conditional Access settings.
- Click Next.
- Select Use Azure AD Conditional Access to protect labeled SharePoint sites.
- Select Allow limited, web-only access. (or Block access if that’s what you want to achieve)
- Click Next twice. (skip the Schematized data assets page)
- Review you’re settings and click on the Create Label button to finish.
Do not apply the Sensitivity Label to SharePoint sites yet; we need to do some additional configuration.
Verify tenant access control setting
Before we proceed further, let’s verify the status of our tenant-wide SharePoint Online access control setting first. Download and connect to the SharePoint Online Management Shell and use the following cmdlet;
| Get-SPOTenant | Select-Object -ExpandProperty ConditionalAccessPolicy |
When AllowLimitedAccess or BlockAccess appears in the output, it means that the global setting for enforcing app restrictions with conditional access policies is configured to limit or block access to unmanaged devices.
On the other hand, if you see AllowFullAccess in the output, it means that our conditional access policies are not restricting access to SharePoint sites by default, unless we apply a Sensitivity Label to them. This is the expected output, unless the setting has been modified in the past.
Make sure that the global setting is set to be less restrictive than what you define in your Sensitivity Labels. Otherwise, the labels will not enforce more restrictive access controls.
To change the setting back to AllowFullAccess, use the following cmdlet;
| Set-SPOTenant -ConditionalAccessPolicy AllowFullAccess |
Configure Conditional Access policy
Let me first explain the function of the Conditional Access policy we’re about to set up. This policy will apply to users who sign in to SharePoint Online, but the restrictions will only take effect if all of the following conditions are met;
- The user tries to access data from a specific SharePoint site.
- The SharePoint site has a label with limited web-only access controls.
- The user is working from an unmanaged device.
If the restrictions take effect, users cannot download attachments, print or sync files, or access files through desktop apps such as Microsoft Office.
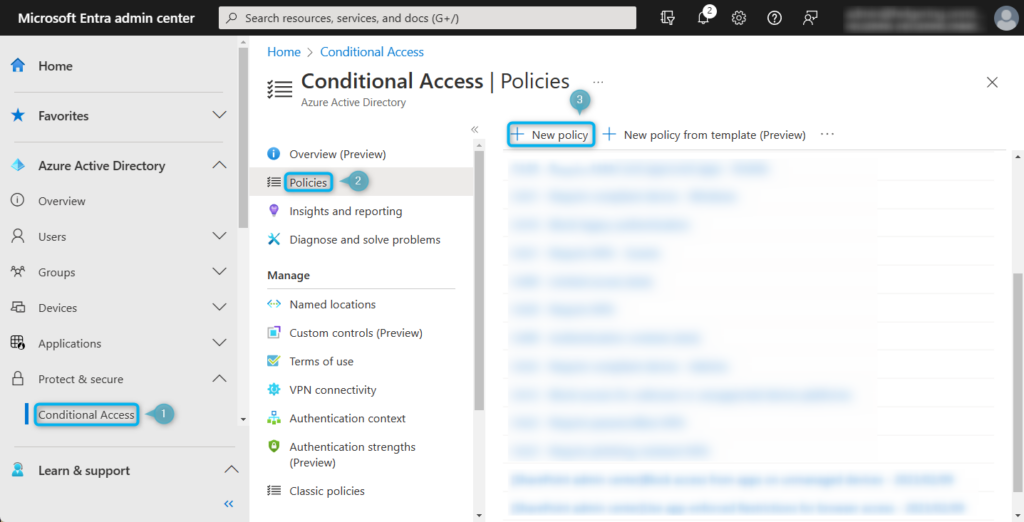
Now that you know what the policy does, let’s configure it by following these steps;
- Navigate to Microsoft Entra admin center > Protect and Secure > Conditional Access
- Go to Policies.
- Click on the + New Policy to create a new Conditional Access Policy.
- Configure the Conditional Access Policy as described in the table below.
| Name | Give the policy a name that fits your company’s naming convention. |
| Users | Select a group of users to apply the policy to. |
| Cloud apps or actions | Select the SharePoint Online cloud app. |
| Conditions | {empty} |
| Grant | {empty} |
| Session | Select the Use app enforced restrictions setting. |
You can safely turn on the policy now because the app-enforced restrictions will only take effect once we apply Sensitivity Labels to SharePoint or Microsoft team sites.
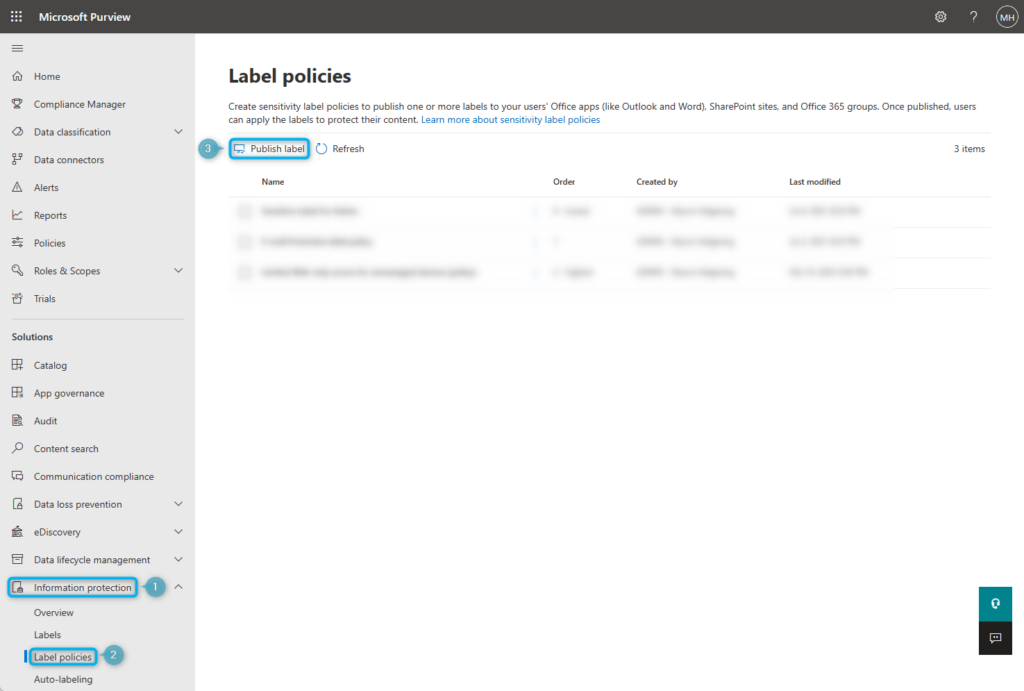
Configure Sensitivity Label policy
Next, we will create a Sensitivity Label policy; this way, we can decide who can label sites or teams.
- Navigate Microsoft Purview (former Compliance Admin Center) > Solutions > Information Protection.
- Go to the Labels policies page.
- Click on Publish label to create a new label policy.
Optional: If you already have existing label policies, you can add your newly created label to one.
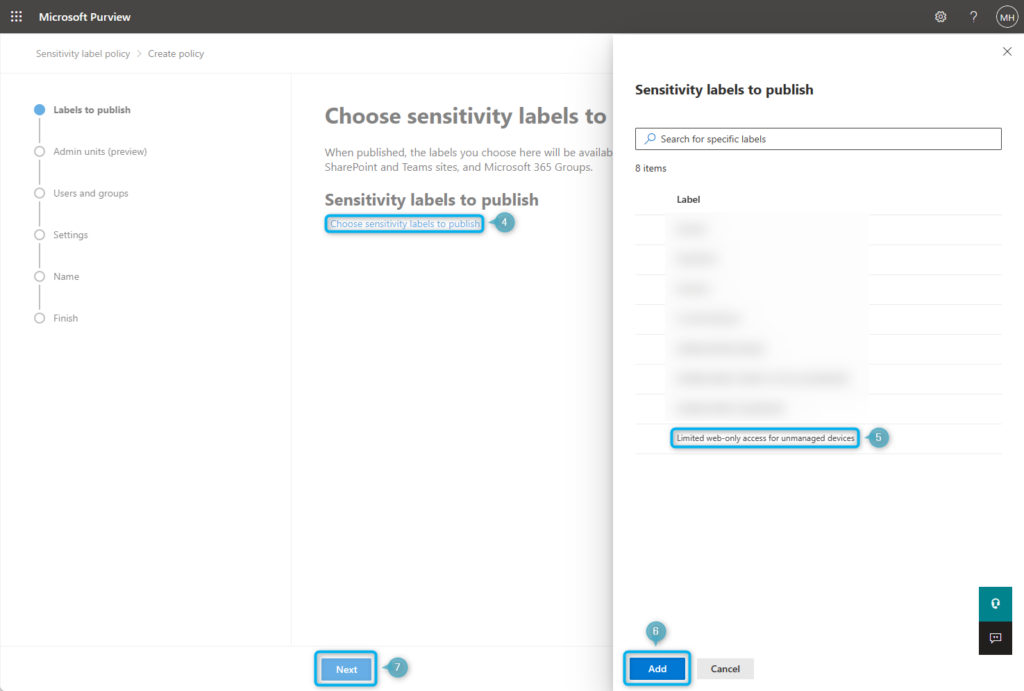
- Click on Choose sensitivity labels to publish.
- Select your newly created sensitivity label. (My example: Limited web-only access for unmanaged devices)
- Click Add.
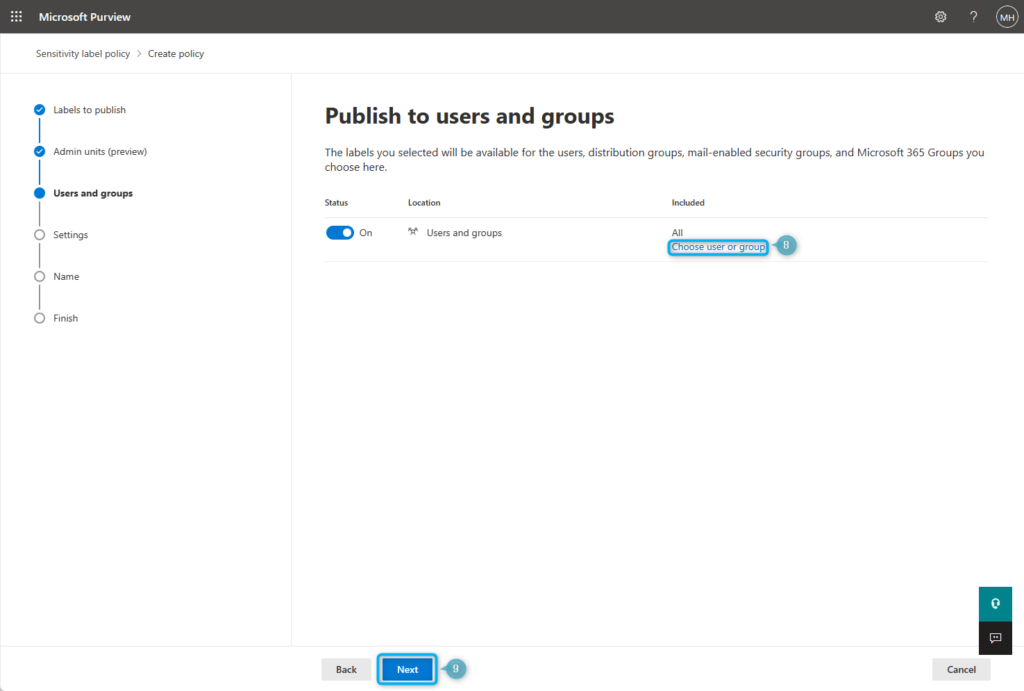
- Click Next twice. (Skip the Admin units page)
- Click on Choose user or group and select the desired users, or alternatively leave the setting on All to include all users.
Note: If it’s part of your governance strategy to let users create sites and teams themselves, you may need to push these labels to all (or most) users. If only admins or key users are allowed to create sites and teams, then you can publish them to a specific group.
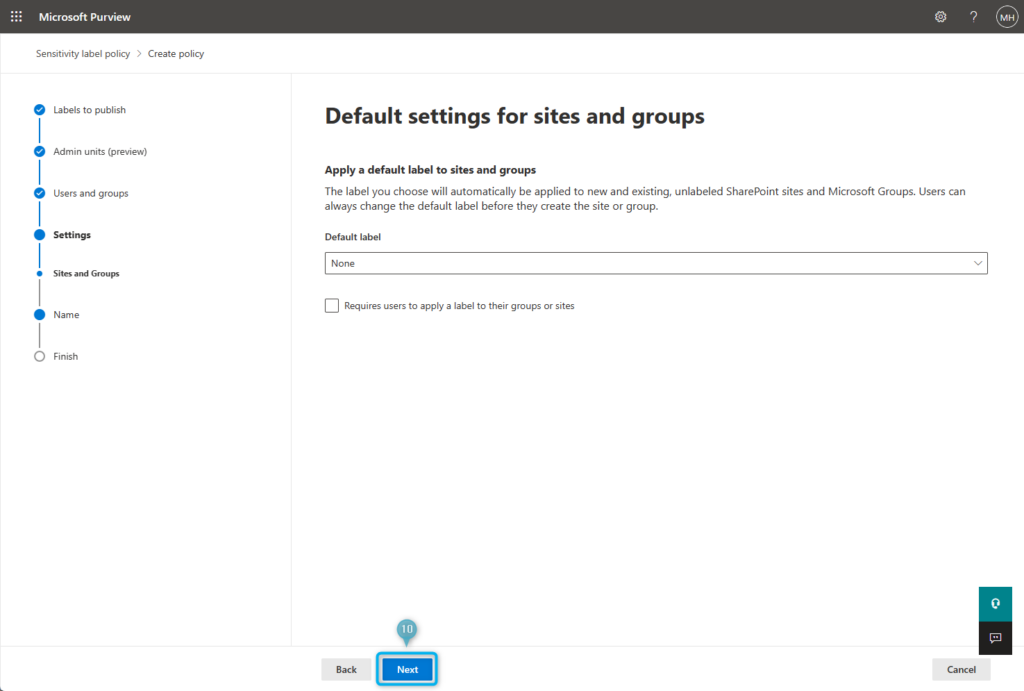
- Click Next twice. (skip the Settings page)
Optional: If you want, you can set the newly created label as the default label or require users to apply a label to their groups or sites. These options are better used when dealing with multiple labels under a label policy, so I wouldn’t recommend using these if your goal is to label the sites yourself.
- Click Next.
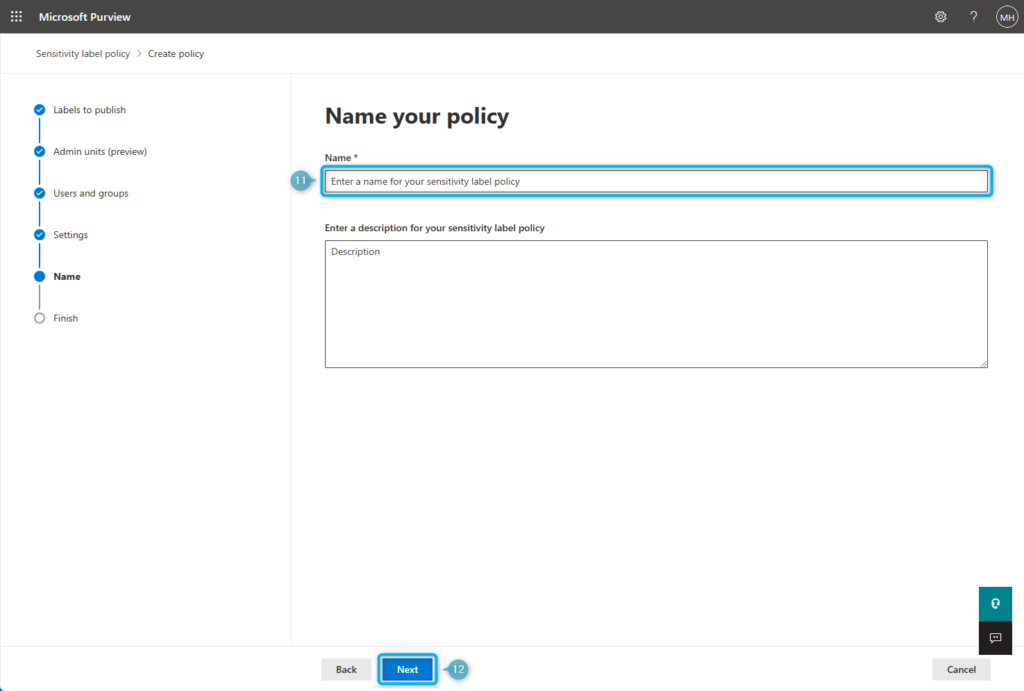
- Enter a Name for your policy.
Optional: Enter a Description for your policy.
- Click Next and Submit to create the Sensitivity Label policy.
Now that the policy has been created, users can apply labels when creating a site or team. Please note that it can take up to 24 hours for labels to show up, so you must be patient.
Apply label to sites (as an admin)
If you, as an admin, want to label existing teams or sites, it is required for you to have one of the following roles or permissions assigned;
- SharePoint Administrator role; to be able to label sites from the SharePoint Admin Center.
- Teams Administrator role; to be able to label teams from the Microsoft Teams Admin Center.
- Site Admin permission; to be able to label an individual site from the SharePoint site information settings.
Follow these steps to apply the label by using the SharePoint Admin Center.
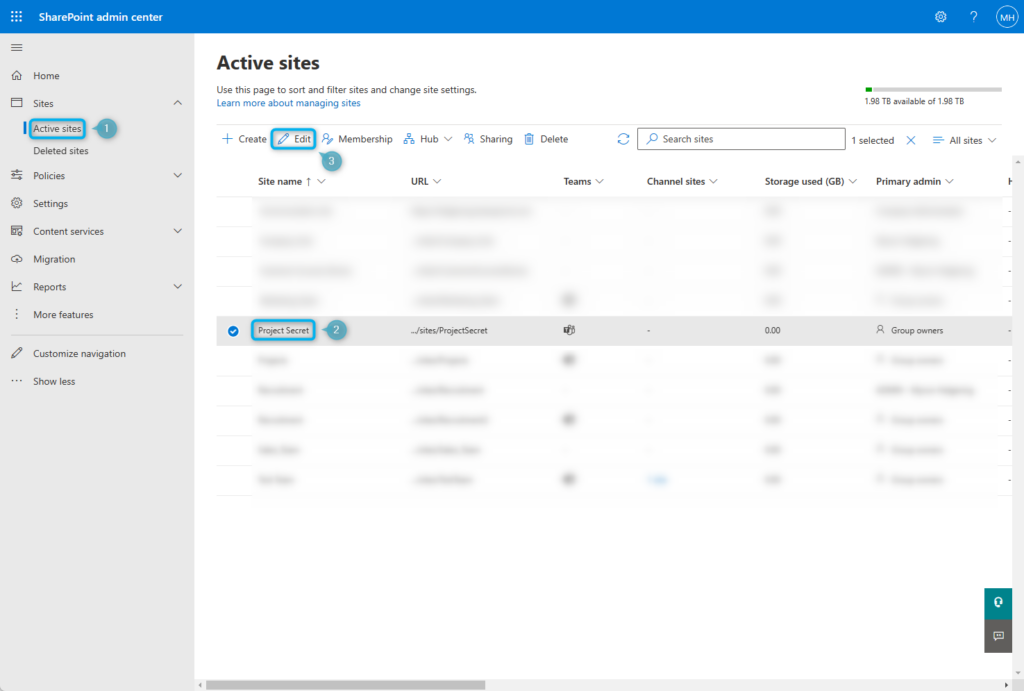
- Go to the SharePoint Admin Center and navigate to Sites > Active Sites.
- Select the Site.
- Click on Edit.
- Go to Settings.
- Select the newly created label.
- Click Save.
We can also use PowerShell to apply labels to multiple sites at once, which can be more efficient than applying labels to sites individually.
Apply label to sites (as an user)
If a user is a member of the sensitivity label policy, they can label sites and teams now. If users cannot create sites or teams, you should check if the creation of sites or teams is enabled for them.
When creating a new team in Microsoft Teams, the user has the option to select the Sensitivity Label for the team.
When creating a new site in SharePoint Online, the user has the option to select the Sensitivity Label for the site.
User Experience
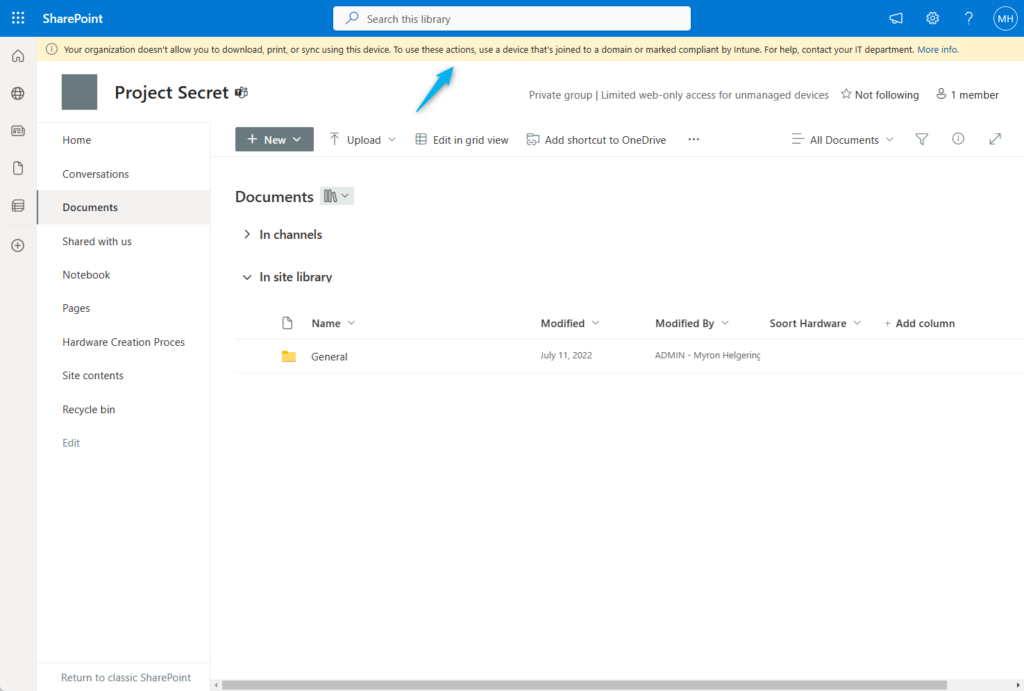
If we look at the team site after applying the label, we will notice a yellow bar at the top of the page indicating that our site is now protected, and users cannot download, print, or sync using unmanaged devices.
Users attempting to access the content from a desktop app, such as MS Word, on an unmanaged device will be unable to access these resources.
Wrap up
To wrap up this post, consider using Sensitivity Labels to enforce limited web-only access, but only if your organization is ready. Your users or admins will have to label previously and newly created sites and teams.
Also, you should know that this method only covers SharePoint data, not OneDrive and Exchange Online data. You should use session policies to bridge this gap.
| This post is part of the unmanaged devices blog series; find more posts here. View previous part: Limited access with conditional access for unmanaged devices View next part: Limited access with session policies for unmanaged devices |
Limited Access with Sensitivity Labels for Unmanaged Devices
Would you like to share your thoughts?
Your email address will not be published. Required fields are marked *





6 Comments