Manage Conditional Access exclusions with Access Reviews
Today, I’m following up on a recent blog post where I talked about how to manage Conditional Access exclusions with PIM. For a similar purpose we are going to utilize the Access Reviews feature, which is part of the Identity Governance solution available in Microsoft Entra.
Access Reviews are a useful tool that helps to ensure the right people have access to the correct applications, admin roles, or group memberships. When used effectively, Access Reviews can minimize excessive access in your environment for both employees and guests.
When it comes to Conditional Access exclusions, IT often struggles to keep track of the list of excluded users. After a user has been excluded for more than a few months, it’s likely that no one remembers why they were added in the first place. This is where Access Reviews come in, allowing us to manage these exclusions, provide insight into account activity, and automatically remove exclusions.
Beyond managing Conditional Access exclusions, Access Reviews can also be used to;
- Manage members or guests membership in Microsoft Teams.
- Manage permissions for SharePoint sites.
- Manage access to enterprise applications.
- Manage eligible or permanent administrative roles in Azure or M365.
- Manage other policy exclusions in for example Microsoft Intune.
In this blog post I am going to show you how you can manage Conditional Access exclusions with Access Reviews and it will include the following sections;
- Scenario
- Licensing and roles
- Prepare Conditional Access policy
- Create Access Review
- User Experience
- Conclusion
Scenario
For this particular scenario, the company has implemented a simple Conditional Access policy that requires MFA for all users. To manage the exclusions for this policy, they have created a security group, allowing members of the group to bypass the MFA requirement.
However, after a few of months, the Security Officer has become concerned about the number of users being excluded from MFA and the potential security risks this poses. When the Security Officer (Albus) asks one of the IT employees (Draco) why the users have been excluded, the IT employee admits that some of the users have been excluded for such a long time that he is no longer certain.
To help the Security Officer effectively manage these exclusions, we will configure a recurring monthly Access Review and require a justification for each exclusion.
Licensing and roles
To meet the licensing requirements for this scenario, you will need the following;
- Azure Active Directory Plan 1; for all users assigned to a Conditional Access policy.
- Azure Active Directory Plan 2; for all users performing Access Reviews.
To be able to create Access Reviews, you’ll also need one of the following roles;
- User Administrator
- Identity Governance Administrator
- Privileged Role Administrator (for role-assignable groups only)
Prepare Conditional Access policy
To follow along, ensure that you have created a Security Group and added it as an exclusion to your Conditional Access policy. We will be using the same policy and group displayed in the picture below.
Create Access Review
To begin, let’s create and configure a new Access Review from the Microsoft Entra admin center.
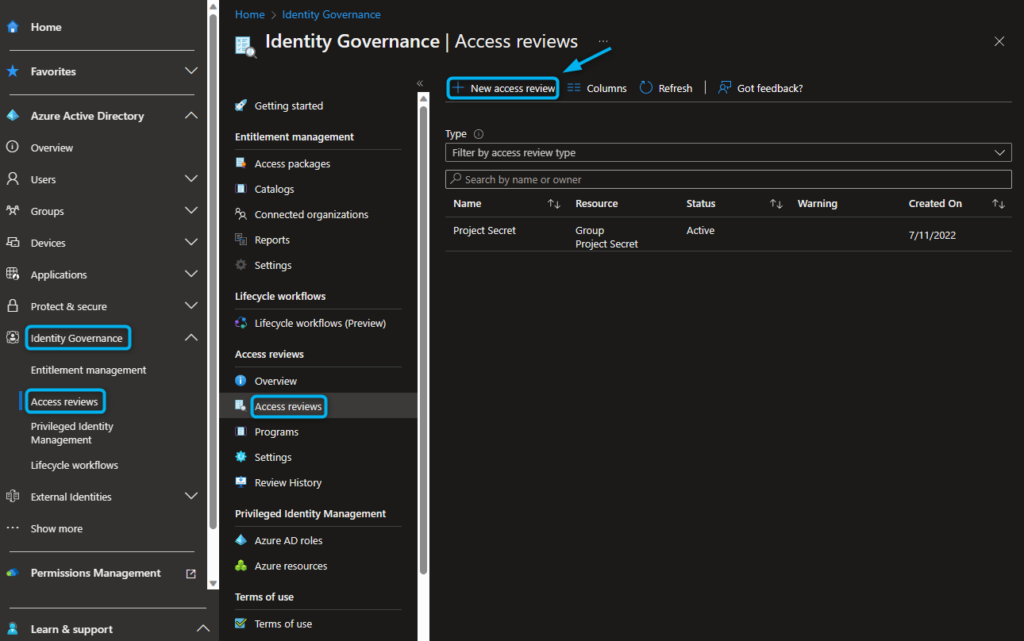
- Navigate to the Microsoft Entra admin center > Identity Governance > Access Reviews.
- Navigate to Access Reviews > and click on + New Access Review.
The first page allows us to configure the scope of the access review. For example, we can choose whether we are reviewing access for applications, teams, and groups, or which users or guests we want to include.
- Select Teams + Groups.
- Set the Review scope to Select Teams + groups.
- Select the “Security Group” that is used for Conditional Access exclusions.
- Set the scope to All users.
- Click Next: Reviews.
On the second page, we can configure who will perform the review and when it will take place.
- Optionally, you can set up multiple stages for the Access Review, with a maximum of three stages.
- Select Selected user(s) or group(s).
- Choose the “users or user groups” who will be responsible for reviewing the Conditional Access exclusions. In my example, I have selected the highly responsible IT employee, Draco.
- Specify the “Duration of the Access Review (in days)”, which specifies the amount of time reviewers have to complete the review. In my example, I’ve set the duration to 7 days.
- Select the Review recurrence, for my example I chose for a Monthly review.
- Choose the Start date of this Access Review.
- Select the End date, which I set to Never.
- Click Next: Settings.
On the third and final configuration page, we will configure the Access Review settings, which includes setting up notifications, justifications requirements and how to handle review results.
- Select Auto apply results to resource to automatically remove the exclusions after the Access Review.
- Decide what will happen “If reviewers don’t respond”. I will select No change option, because removing valid exclusions could have negative consequences such as the malfunctioning of applications or the breaking of automated tasks.
- Choose whether to send a notification at the end of the review. I decided to notify our Security Officer, Albus, as he will be interested in knowing the outcome of the Access Reviews.
- Select No sign-in within 30 days to present information about inactive users to the reviewer. This information could help determine if exclusions are still necessary.
- Select Justification Required to make sure reasons for approval are logged for auditing purposes.
- Select E-mail Notifications to make sure reviewers know when it is time to review.
- Select Reminders to remind reviewers that they still have an active access review to finish.
- Supply some extra context as to why this Access Review needs to be completed.
- Click Next: Review + Create > give the Access Review a name and click Create.
After configuring the Access Review, we can now wait for the recurring review to begin. In our example, we started the review today, so let’s see what we have set in motion.
User Experience
Our trustworthy IT employee, Draco receives an e-mail requesting him to review the Conditional Access policy exclusions. Upon clicking the Start Review button, he is redirected to the myaccess page, where he can perform the Access Review.
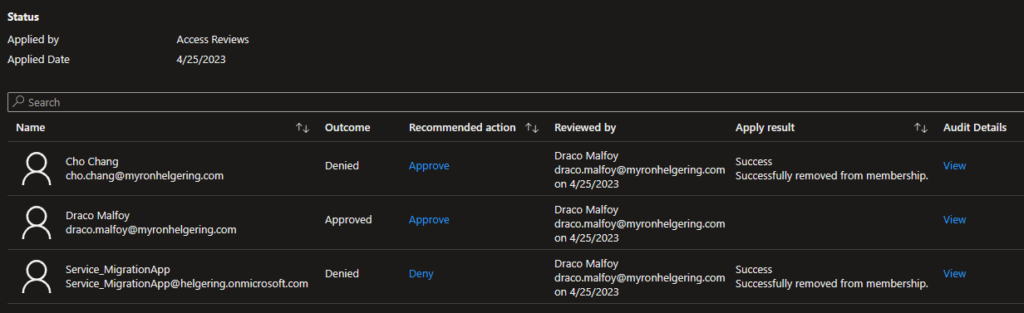
Draco is presented with a list of excluded users from the Conditional Access policy, and must choose to either approve or deny their membership access to the security group. Additionally, he notices a “Recommendation” for the Service_MigrationApp account, indicating that this user has not logged in recently.
Draco provides justifications for each user in the list as he makes a decision for them.
After the Access Review, which we set to run for a duration of 7 days, has been completed, any user who was denied access will be automatically removed from the security group. This ensures that the Multi-Factor Authentication CA policy is enforced again for these users.
After the Access Review has been completed, an email will be sent to our Security Officer, Albus, notifying him of the completion of the review.
When he checks the results of the monthly Access Review, he discovers that Draco has approved his own exclusion.
After reviewing the audit details, Albus determines that Draco provided a non-valid reason for his exclusion, and as a result, he can take the appropriate actions.
Conclusion
In my experience Access Reviews can be an efficient method to manage Conditional Access exclusions. When combined with just-in-time exclusions with Privileged Identity Management, you will probably reduce the amount of exclusions significantly. Even though we may not be able to completely eliminate them, at least we can be sure that each exclusion has a valid reason and we can work towards reducing the amount constantly.
Manage Conditional Access exclusions with Access Reviews
Would you like to share your thoughts?
Your email address will not be published. Required fields are marked *












2 Comments